An in depth look at the future of the EV cybersecurity industry.
The EV industry as a whole is projected to grow immensely over the next five years. Influenced by governmental regulations attributed to environmental concerns and the global shift of interest in increased connectivity, this does not only impact the OEMs and Tier 1 Suppliers manufacturing the vehicles but the public (i.e. government funded transportation agencies) and private sectors (i.e. automotive manufacturers selling to individuals) establishing the infrastructure needed to allow electric vehicles on the road, for example the grid, networks, and charging stations, etc. As a fairly young industry, the electric vehicle industry has a lot of learning curves, however the popularity of these vehicles will outpace the needed regulations to make EVs efficient. The US is not the only initiative by a region taking place to make the shift to EVs, Europe plans to make the transition fully by 2035, meaning the EV charging station industry, alongside the electric vehicle market is expected to grow immensely.

With these changes in the industry already taking place car manufacturers are focused on integrating the most advanced technologies into their vehicles, taking connectivity and efficiency into consideration. Government automotive security regulations are already in place for over 100 countries and even more government regulations are expected to take place.
There are a range of stakeholders in the electric vehicle industry including car manufacturers, charging station manufacturers and operators, power grids, and the end user (the driver and passengers of the vehicle). Threats in the automotive industry have grown exponentially as developments in technology have integrated into the systems, transforming vehicles to computers on wheels. Cybersecurity is essential to the everyday lifecycle of vehicle development, the charging stations, the power grids, and everything in between dealing with EV infrastructure. All the pieces to the EV puzzle hold data which is extremely valuable. As this data becomes increasingly valuable and we see hackers showing heightened interest, initiatives across all the stakeholders (governments, automotive manufacturers and more). The need to take initiative to implement effective cybersecurity measures is evident.
The next generation of cybersecurity solutions for the automotive industry will accommodate the computer on wheels, known as the software-defined vehicle. The automotive industry must learn how to manage software at scale. Ever-evolving software updates and cyber regulations, a shortage of relevant experts, and increasingly complex processes make automation essential in the modern product lifecycle. The industry needs a platform that automates the automotive security lifecycle, including legacy vehicles and efficiently manages vulnerabilities from end to end, while streamlining and connecting the development process to operations. This platform along with keeping the vehicles secure will help automotive companies remain competitive and provide more business value while supporting the complex, multi-vendor mobility ecosystem through sharing and collaboration of cybersecurity, inside the organization and with suppliers.
Automotive manufacturers across the board are implementing more connected technologies into vehicles, as an example 5G connectivity in the infotainment center of the vehicles. The need for cybersecurity implementation across the development lifecycle of the automotive industry is critical and automotive companies are recognizing this. With government regulations requiring auto manufacturers to implement features such as cameras, automatic brakes, and lane drift warning systems, the opportunities for cybersecurity implementation have only expanded and will continue to expand. This implementation is no longer an indulgence, rather a necessity and due to the lack of cybersecurity professionals, auto-manufacturers are at a standstill.
The regional landscape of the automotive industry has definitive impacts on cybersecurity implementation. In recent years the Asia Pacific auto-manufacturers have dominated the industry with being the firsts to integrate new groundbreaking technology into their vehicles. However, with this implementation, the need for cybersecurity is ever-growing. India is another dominant market producing for consumer demanded EVs, and China’s market is rapidly growing in the EV industry as well. Alongside the Asia Pacific region, European car manufacturers are also showing heightened interest in manufacturing EVs, especially with government regulations imposed to ban non-EV vehicle manufacturing by 2035. North American automotive manufacturers will also prioritize EV production, which creates a market rife with possibilities for potential cyberattacks, making cybersecurity implementation absolutely necessary for the future market. Although there are few occurrences with immediate impact, the future impacts of cybersecurity breaches are insurmountable.
Where cybersecurity implementation differs for regular automobiles to EVs is data protection. Although hackers are able to access regular automobiles via connectivity and infotainment centers the risk exponentially increases in EVs as they are connected to a grid in the charging stations which opens the gates for hackers to come in from multiple entry points. There is also an expanded list of stakeholders in the EV industry which is inclusionary of cybersecurity solution providers, Tier-2 suppliers, Tier-1 suppliers, and the OEMs. All these stakeholders work together to provide a functioning product to the end-user.
Electric vehicles are more susceptible to attacks than regular vehicles due to the way their connectivity works which also includes external connections to charging stations. With the intricacies of IoT if a hacker gains access to an EV they can then access any charging station the EV attaches itself to and furthermore gain access to any other EV that charges at the same stations, a similar affect as the COVID infection spread we saw in the beginning of 2020. With this widespread hacking being able to take place hackers could then gain access to the whole electricity grid and access personal information of the end user and more powerful entities.
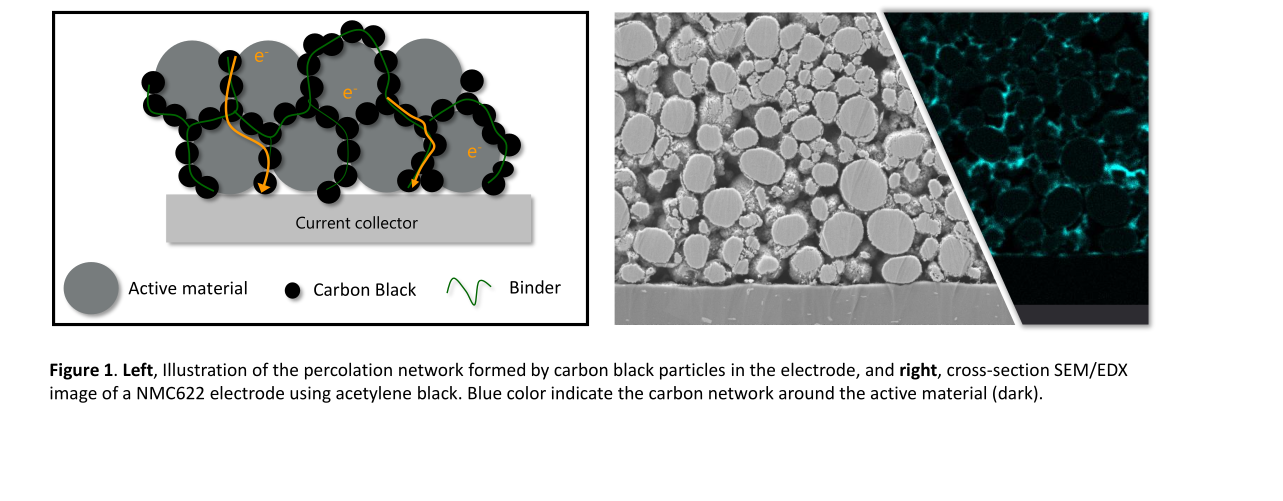
For an effective cybersecurity solution to work, EV cybersecurity companies need to take into consideration the ECUs, charging management and battery management. Charging management is referencing the larger entities growing around this industry such as charging stations and the electricity grid. Battery management is referencing the software implemented into the EV that operates all the things involving the vehicle, including the motor. When charging and battery management are unprotected, it leaves a lot of room for error on the side of the cybersecurity providers and it is essential that the solutions are scalable not only as new threats arrive but to allow room for further development for the OEMs and Tier 1 suppliers to focus on other areas of business development. It is essential for these stake holders to have adaptable automated solutions in cybersecurity so they can continue to fulfill the needs of the industry.
Raz Meridor, EVP Product & Strategy, C2A Security